Featured
Table of Contents
- – What Is A Vpn Tunnel?
- – What Is A Vpn Tunnel, And How It Works?
- – Vpn Protocols Explained – Which One Should Yo...
- – Vpn Tunnel: What Is It & Why Cyberghost Is Th...
- – Understanding Vpn Ipsec Tunnel Mode And ...
- – What Is Openvpn? - Openvpn
- – Vpn Tunnel: What Is It & Why Cyberghost Is T...
- – What Is A Vpn Tunnel And How It Works - Xvpn
- – What Is A Vpn? How Does It Work And Why Do Y...
What Is A Vpn Tunnel?
The strength of a tunnel depends upon the type of tunneling procedure your VPN supplier uses. Some protocols are outdated and might not supply data encryption that is strong enough to deter online snoops so it's a good concept for you to deal with a VPN service provider that relies on the greatest possible tunneling procedure.
That locks out many potential users. If you're searching for the strongest defense while online, you need to think about investing in a VPN company that relies on the Open, VPN procedure. This protocol deals with all the major operating systems, Linux, Window, and Mac, on the mobile os of Android and i, OS.
What Is A Vpn Tunnel, And How It Works?
His work has actually appeared in the Washington Post, Chicago Tribune, and Fox Business. Our offerings may not cover or protect versus every type of criminal activity, scams, or risk we compose about.
The humble VPN has actually become progressively popular in current years, primarily since they have the capability to bypass federal government censorship and geo-blocked websites and services. Better still, a respectable VPN will permit you to do this without offering away who is doing the bypassing. In order for a VPN to do this, it produces what is understood as a tunnel in between you and the internet.
When you link to the web with a VPN, it develops a connection in between you and the internet that surrounds your web information like a tunnel, securing the data packets your device sends out. While technically developed by a VPN, the tunnel by itself can't be thought about private unless it's accompanied with file encryption strong enough to prevent governments or ISPs from intercepting and reading your internet activity.
Vpn Protocols Explained – Which One Should You Use?
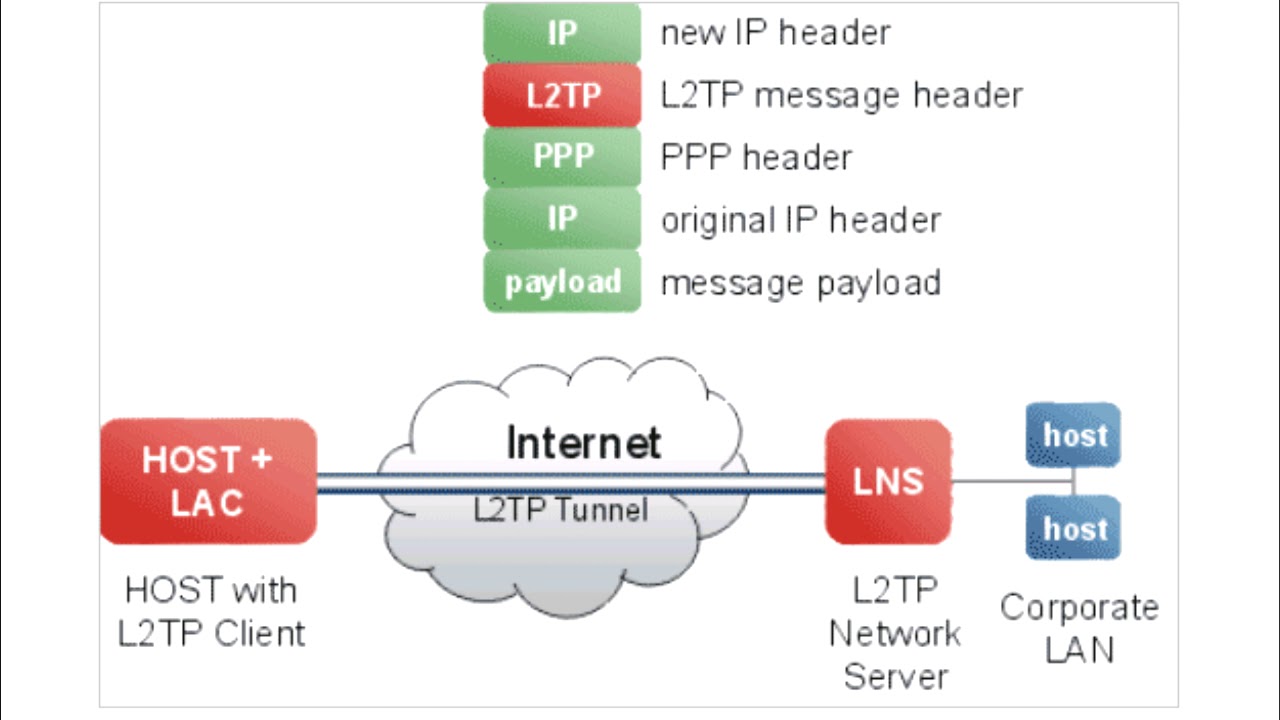
There are lots of kinds of VPN protocols that deal varying levels of security and other functions. The most frequently used tunneling procedures in the VPN industry are PPTP, L2TP/IPSec, SSTP, and Open, VPN - and the world's best VPN services must use most or all of them. Let's take a more detailed look at them.
As a Windows-based tunneling procedure, SSTP is not readily available on any other operating system, and hasn't been separately examined for possible backdoors constructed into the procedure. Saving the very best for last, we have Open, VPN, a reasonably current open source tunneling procedure that utilizes AES 256-bit encryption to safeguard information packages.
Vpn Tunnel: What Is It & Why Cyberghost Is The Best
An excellent VPN service ought to use you the option of at least these four kinds of tunneling protocols when going on the internet. When it comes to the finest VPN to sign up for there are plenty of choices to pick from. Naturally, if cash is tight and you're not too crazy about spending anything more than you need to, trying the very best low-cost VPN could be an option.
The main problem with opting for a free VPN is that you generally will not get the exact same worth as that supplied by a paid-for rival. What's more, if you're utilizing a VPN then one of the primary considerations is going to revolve around security.
Understanding Vpn Ipsec Tunnel Mode And ...
Free VPNs can be a little miserly when it comes to the quantity of data you can use, with the running speed often being less remarkable than paid-for alternatives too. If you have actually got a desire to stream video or are torrenting on a routine basis, this may be false economy.
Tech, Radar Pro developed this content as part of a paid partnership with Express, VPN. The contents of this post are totally independent and solely show the editorial viewpoint of Tech, Radar Pro.
What Is Openvpn? - Openvpn
While it's challenging to set up by itself, Open, VPN is terrific for speed, security, and encryption. Express, VPN users can toggle in between UDP (optimal for speed) or TCP (ideal for connection dependability.)Among the more recent VPN procedures offered to consumers, IKEv2 is thought about to be a lighter and more stable alternative than Open, VPN.
Due to its absence of file encryption and authentication features, PPTP is the fastest VPN protocol. This indicates that your internet traffic can be seen by third celebrations. We do not advise utilizing PPTP, and it is no longer supported on Express, VPN apps.
Vpn Tunnel: What Is It & Why Cyberghost Is The Best
Table of contents It's simply plain scary to believe about, isn't it? The unfortunate reality is, this is just how your connection to the internet works it's like an open window into the goings on in your house, and any nosey parker can peep through. Whether it's your Internet Service Service Provider (ISP) seeking to track and sell your information to marketers, or dishonest hackers attempting to take your personal information to offer on the dark web, it often seems like the entire world has a beneficial interest in sleuthing on your online activity.
There are a number of methods to ward off potential online snoopers, one of which includes using a Virtual Personal Network (VPN). In a nutshell, VPNs assist you browse the web safely, independently, and without any restrictions. (We have actually already waxed lyrical on the advantages of using a VPN in the past, so we will not harp on again too much here).
What Is A Vpn Tunnel And How It Works - Xvpn
Essentially, they are a series of numbers utilized to secure and decrypt data just they have access to. Hey, dropped connections take place in some cases, even to the absolute best (and most expensive) VPNs. This is why most trusted VPN service providers come with a seriously useful function an automatic kill switch. Think of the kill switch as your last line of defense a digital guard standing constantly on guard, monitoring your connection to the server.
Tunneling utilizes a layered protocol design such as those of the OSI or TCP/IP protocol suite, however normally breaks the layering when utilizing the payload to carry a service not generally offered by the network. Generally, the shipment procedure operates at an equivalent or higher level in the layered design than the payload protocol.
What Is A Vpn? How Does It Work And Why Do You Need ...
Another HTTP-based tunneling technique uses the HTTP CONNECT method/command. A client concerns the HTTP CONNECT command to an HTTP proxy. The proxy then makes a TCP connection to a particular server: port, and passes on data between that server: port and the client connection. Because this creates a security hole, CONNECT-capable HTTP proxies commonly limit access to the CONNECT technique.
Even though the SMB protocol itself consists of no encryption, the encrypted SSH channel through which it takes a trip offers security. Local and remote port forwarding with ssh executed on the blue computer system. When an SSH connection has actually been developed, the tunnel begins with SSH listening to a port on the remote or regional host.
Table of Contents
- – What Is A Vpn Tunnel?
- – What Is A Vpn Tunnel, And How It Works?
- – Vpn Protocols Explained – Which One Should Yo...
- – Vpn Tunnel: What Is It & Why Cyberghost Is Th...
- – Understanding Vpn Ipsec Tunnel Mode And ...
- – What Is Openvpn? - Openvpn
- – Vpn Tunnel: What Is It & Why Cyberghost Is T...
- – What Is A Vpn Tunnel And How It Works - Xvpn
- – What Is A Vpn? How Does It Work And Why Do Y...
Latest Posts
Best Vpn Services 2023 - Expert Tested And Reviewed
The Best Vpns For Businesses And Teams In 2023
Best Vpns For Business Travelers To Stay Digitally Fit (2023)
More
Latest Posts
Best Vpn Services 2023 - Expert Tested And Reviewed
The Best Vpns For Businesses And Teams In 2023
Best Vpns For Business Travelers To Stay Digitally Fit (2023)